Advanced Threat Intelligence
Safetech enables organisations to seamlessly identify and mitigate threats with real-time, unbiased and actionable threat intelligence.

Why Is Threat Intelligence Important for your business?
Threat intelligence is crucial for modern cybersecurity to allow organisations to proactively defend against potential attacks.
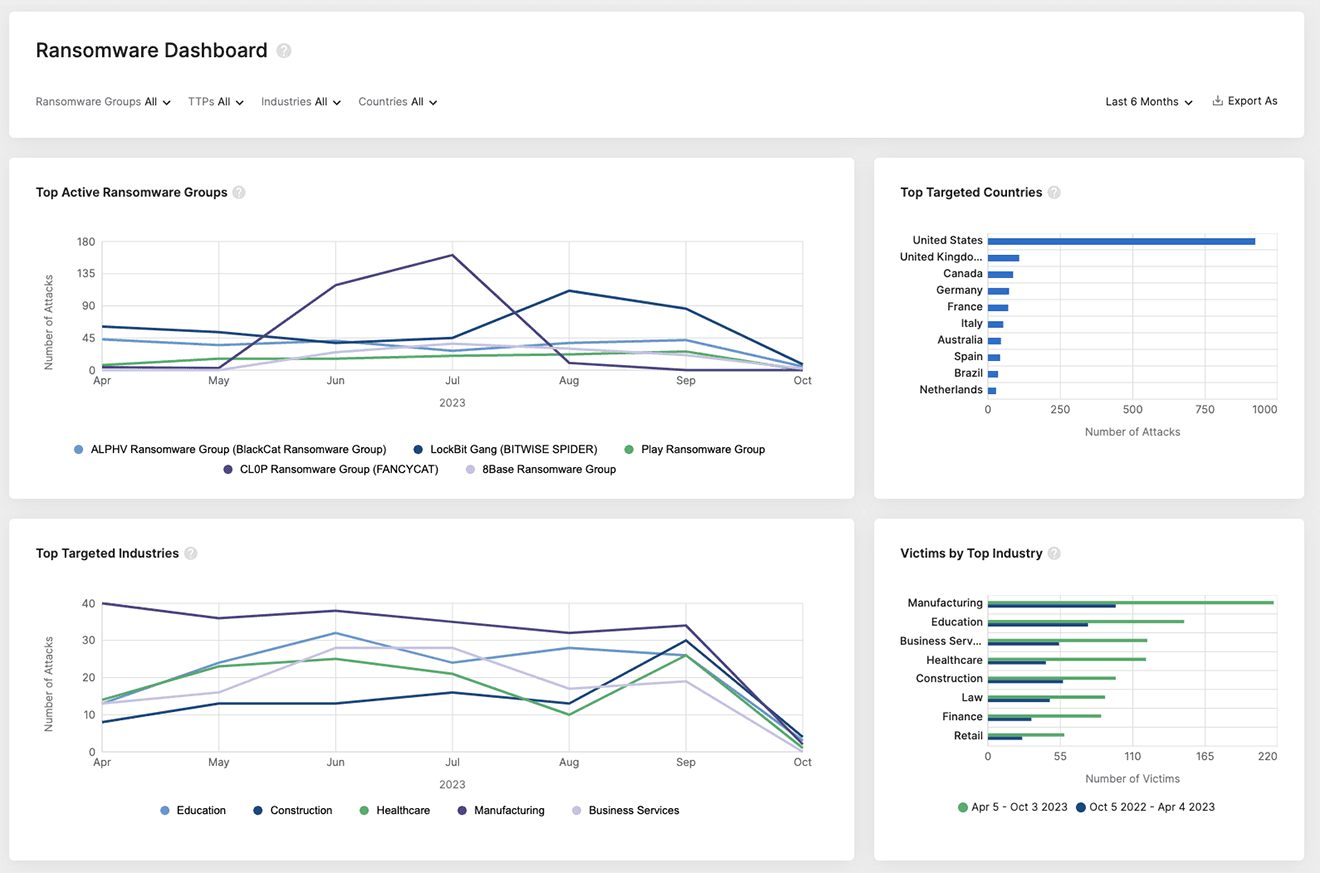
By understanding threat actors and their tactics, techniques, and procedures (TTPs), our security teams can anticipate and mitigate your threats before they materialise. It provides actionable insights, helping prioritise threats and allocate resources effectively.
Integrating threat intelligence with your existing security stack enhances your detection of advanced threats and accelerates your incident response. Staying informed about emerging threats and vulnerabilities enables timely patches and risk reduction.
Do you know your attack surface?
Did you know that 76% of organisations experienced an attack that started with the exploit of an unknown or improperly managed internet-facing asset. Your attack surface is growing and changing, requiring real-time visibility for awareness.
We spot your threats early with our leading Dark Web Monitoring Service
Threat Alerts
Get threat tailored alerts, including leaked credentials, open ports, code repos, and software vulnerabilities.
Criminal Activity
Receive automated alerts when your brand or its employees are mentioned by threat actors or groups.
Hidden Threats
Identify indicators of insider threats, the sale of initial access on hacking forums, ransomware group listings, and supply chain attacks.
Continuous Monitoring
AI-powered scanning of your attributes, including domains and IP addresses.